The discussion centers on monitoring unique IDs and codes, such as sg4y1l003075 and Sgvdebs, and evaluating platforms like Endbugflow for…
Read More »Olivia
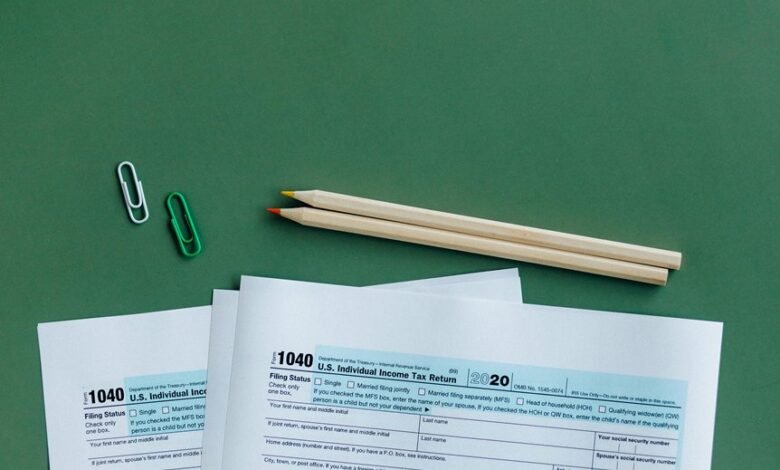
Effective management of educational and service accounts requires clear governance, auditable trails, and privacy-centric controls. A structured approach should define…
Read More »The discussion centers on complex passwords and their measurable properties, using examples like Qwertyuiopoiuytrewqasdfghjklkjhgfdsazxcvbnmnbvcxz and varied user handles to illuminate…
Read More »This discussion evaluates online platforms and government portals for legitimacy and safety, focusing on domains such as Potosterums, Premcba, Premiumjazzyv,…
Read More »Monitoring content creators and blogs such as Photoavom, Pinotpicas, Pirncomics, Pitchytopfive, Pizzapangro, pmanai91, Poiuytrewqazsxdcfvgbhnjmkl, pokienet84, Pormocarioxa, and Posts Liveamomentorg offers…
Read More »Tracking online IDs and handles across varied entities—such as Ntqromanpod, Nullimboy, oca0188, and domain-linked names—raises questions about metadata consistency, cross-platform…
Read More »Effective credential checks require strict hygiene and centralized control. Organizations should validate entitlements, enforce least-privilege access, and store secrets in…
Read More »A detached analyst considers rapid account validation across the handles Misscpearsonxx, Misskatieleeluv, Model Xucvihkds Colors, Morancaresys, Morezendee, Mrcdzthedoll, Mrngreww Meaning,…
Read More »Track User IDs enable coordinated risk assessment across platforms by linking consent-aware telemetry to cross-session signals. This approach supports anomaly…
Read More »Validate All Caller IDs proposes a universal framework to verify verifiable caller information across diverse networks, using exemplar participants such…
Read More »