Validate Web Portals and Services – Toropprnl, Trannyvodeosx, Transmartproject Amanda Furness Email, Trapstarsxxx, Traveltweaks Phone Number, Trimzbby, tune5801t, Tutorial by Hearthstats Hssgamepad, Tutorials Undergarcade, Tv Model Number rimiot501
Assessing legitimate web portals and services requires a structured approach that covers ownership clarity, verifiable contact details, and independent evaluations, alongside repeatable performance tests across devices to gather objective latency and throughput metrics. A practical checklist with clear pass/fail criteria helps identify scams and confirm domains, while monitoring uptime and user feedback supports ongoing validation. This framework offers a concise starting point, but exposing gaps and improving safeguards invites further scrutiny and discussion.
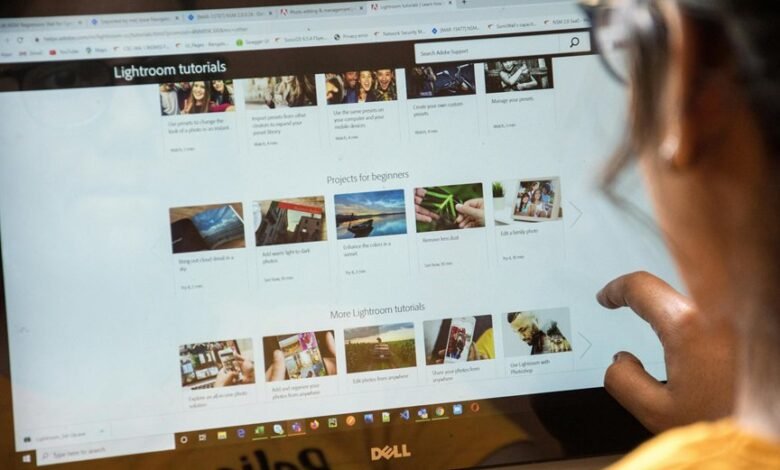
How to Identify Legitimate Web Portals and Services
To identify legitimate web portals and services, one should assess their credibility through clear indicators such as transparent ownership, verifiable contact information, and legitimate security measures. This approach emphasizes independent evaluation, careful cross-checking of claims, and consistent performance history.
The focus remains practical: identify scams, verify domains, confirm uptime, and review user feedback. Structured appraisal supports freedom through informed, cautious engagement.
Key Security Checks to Validate Online Platforms
Are robust security checks essential for validating online platforms, or can superficial assurances suffice?
The evaluation focuses on legitimate portals through structured scrutiny: authentication strength, data handling, and access controls.
Performance testing informs reliability without exposing sensitive flaws.
A disciplined approach reduces risk, ensuring platforms maintain integrity, privacy, and trust while enabling freedom to innovate without compromising user safety.
How to Test Performance Across Devices and Networks
Performance testing across devices and networks requires a systematic approach to quantify user experience under varying conditions. The report outlines objective criteria, repeatable scenarios, and representative networks to capture latency, throughput, and reliability. It emphasizes disciplined data collection, consistent environments, and clear interpretation. Key steps include review benchmarks and cross device testing to compare performance across platforms and endpoints.
A Practical Validation Checklist You Can Use Today
A practical validation checklist enables teams to verify core functionality and performance with concrete, repeatable steps. The checklist outlines objective criteria, traceable test data, and clear pass/fail thresholds, reducing ambiguity. It emphasizes independence from irrelevant, unrelated topic distractions, guiding testers to document results succinctly. By using structured, repeatable actions, teams minimize non sequitur errors and ensure consistent validation across portals and services.
Conclusion
Conclusion: A rigorous validation framework is essential for discerning legitimate portals from risky ones. By confirming ownership, transparency, independent reviews, and solid access controls, while measuring latency, throughput, and uptime across devices, stakeholders gain a reliable trust baseline. This process acts as a lighthouse—steady beacons guiding safe usage amid turbulent, unverified waters. When documentation is concise and traceable, the path to safer engagement becomes clear and navigable for users and operators alike.



